How has Estonia applied Blockchain technology to the e-Government system?
Blockchain is considered as the key technology in e-Government development thanks to its undeniable advantages and potential. From a technical point of view, Blockchain technology increases efficiency, provides data protection and transparency. However, many countries still face certain obstacles when applying Blockchain to e-Government.
In this article, Lina Network will discuss the Blockchain application of Estonia, one of the countries with the highest level of e-Government development. Some of the technical concepts mentioned in the article will be explained in section 6.
▶ What is e-Government? Global e-Government development in 2020
1. Transparency and Confidentiality
When it comes to the advantages of Blockchain technology, transparency and information security are the first that come to mind. However, considering both of these features in e-Government development will lead to certain conflicts.
The main objective in digital data security is confidentiality - the restriction of access to some specific individuals to ensure the information does not fall into the hands of outsiders. Conversely, transparency aims at equality of access to information for all people, while ensuring that the provided information is clear, consistent and reliable. In the context of democratic countries, transparency and accountability often take precedence over confidentiality. In addition, prioritizing confidentiality while ensuring transparency requires complex security protocols, which leads to many difficulties in the operation.
In order to apply Blockchain to digital government, we need to understand the main objective of data protection and how to put it into the context of democratic countries. The way Estonia applies Blockchain technology in e-Government will provide us with valuable insights to answer this question.
2. Why did Estonia choose Blockchain technology?
Estonia started its digital transformation journey more than 20 years ago, and it is the leading country in e-Government development at the moment. Estonia’s goals are to increase the efficiency and transparency of the government apparatus, as well as promoting the economy and improving the overall wellbeing of its citizens. Since the beginning, Estonia has enacted many policies to support the digital society. For instance, in 2000, Estonia declared Internet access to be a human right.
An important part of Estonian legal framework needs to be mentioned is the “once-only principle”: no record of information is stored twice in the system, any updates must be performed on the master record. This is to ensure data integrity, allows checking on history and updates, as well as query records of individual access.
For this reason, it can be seen why the Estonian government uses Blockchain to secure digital data. The transparency and immutability features of Blockchain allow detecting data manipulation, whether the attack is from outside or inside. The information stored on Blockchain’s ledger is almost impossible to be stolen, modified, or deleted, which ensures data integrity.
▶ Learn more about Blockchain technology and its application in 4.0 era.
3. KSI Blockchain
The Blockchain platform used in Estonia is called KSI Blockchain (Keyless Signature Infrastructure), provided by Guardtime. KSI Blockchain is designed to protect the networks, servers and database in Estonia from being attacked, ensure the integrity of data-at-rest, and enable the detection of any intentional or unintentional data modification. This technology has been integrated into many important government registries, such as business registry, succession registry, property registry, digital courts database, etc.
KSI Blockchain is used to create “Proof-of-Existence” for any digital records. Put simply, the documents entered into the system will be hashed into a short string of keys, called a hash value. Then, the hash value, timelog and the signing entity will be written to KSI Blockchain, which creates a “signature” that proves the uniqueness of the document. This practice takes advantage of Blockchain’s non-rewrite feature to ensure data integrity.
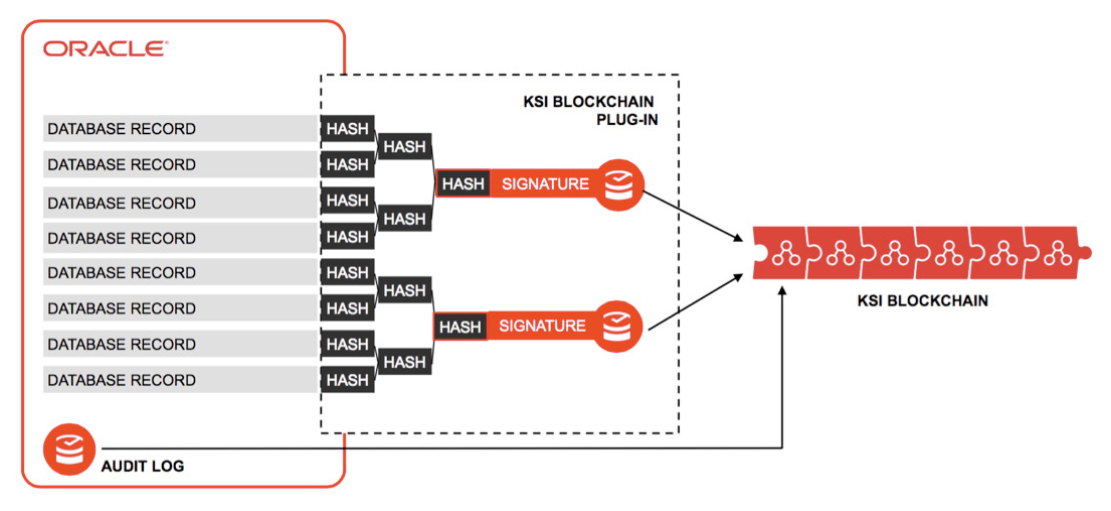
KSI Blockchain protects database records and audit logs (Source: Ivo Lõhmus, Guardtime)
So how does KSI Blockchain solve the problem of transparency and confidentiality? When a document is written into the database, only its hash value is sent to the KSI Blockchain, the original information never leaves the server. This helps ensure the confidentiality of data-at-rest while still allowing the authority to track and trace any data modifications on the system. It is possible to verify the “signature” of the document independently without having to access the original document.
4. KSI Blockchain completes the X-Road framework
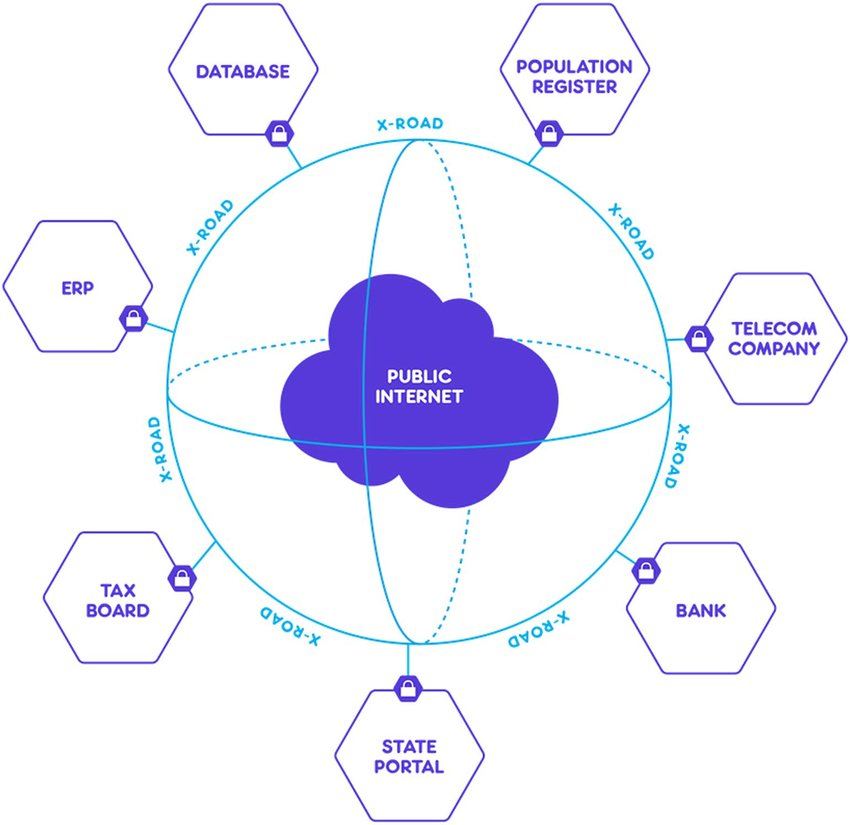
The X-Road digital framework is the reason Estonia can become one of the leading e-Government countries. Put simply, X-Road is a platform connecting various interfaces, servers, and services in Estonia, creating a common layer of information exchange between systems. All Estonian government agencies have to connect their digital systems to the X-Road platform.
X-Road provides a relatively strong information security platform. However, X-Road can only protect the data-in-transit but cannot guarantee the security of data-at-rest. This creates a major security hole: data written into the database can be hacked, modified, deleted, and the audit log cannot be checked. Therefore, the birth of KSI Blockchain plays an extremely important role in ensuring data integrity and enhancing the ability to track every change/ update. However, KSI Blockchain still has the weakness of being unable to protect data-in-use.
5. Conclusion
Thanks to outstanding advantages such as information security, transparency and system efficiency enhancement, Blockchain is chosen by many countries around the world as an e-Government solution, namely Estonia, Switzerland, China, Japan, America, UK, etc. Although the application of Blockchain to optimal government management processes is still facing many obstacles, the potential of this technology cannot be ignored. Estonia’s KSI Blockchain is a prime example of a successful Blockchain application in e-Government.
Subscribe to Lina Network blog to read more interesting articles about Blockchain and other breakthrough technologies:
6. Technical concept explanation
- Confidentiality: Ensuring the information is only accessible for certain authorized individuals.
- Transparency: Ensuring equal access to information for everyone, all data can be clearly verified.
- Data Integrity: Ensuring data is not altered, manipulated or lost during data processing, storage or sharing.
- Proof-of-Existence: A mechanism to verify the existence of a document through hash function.
- Hash Function: An algorithm that generates corresponding hash values for each block of data entered, acting as a key to distinguish different data blocks.
- Data-at-rest: All data is stored in digital form.
- Data-in-use: The data is being processed and has not yet been saved to the digital system.
- Data-in-transit: Data needs to be used in a certain process and is being forwarded from one database to another.
7. References
- European Commission 2018, Case Study Report: e-Estonia, Castaños V., viewed 7th August 2020, <http://www.jiip.eu/mop/wp/wp-content/uploads/2018/10/EE_e-Estonia_Castanos.pdf>.
- Martinovic I., Kello L. & Sluganovic I. 2017, Blockchains for Governmental Services: Design Principles, Applications, and Case Studies, viewed 31th August 2020, <https://www.ctga.ox.ac.uk/sites/default/files/ctga/documents/media/wp7_martinovickellosluganovic.pdf>.


